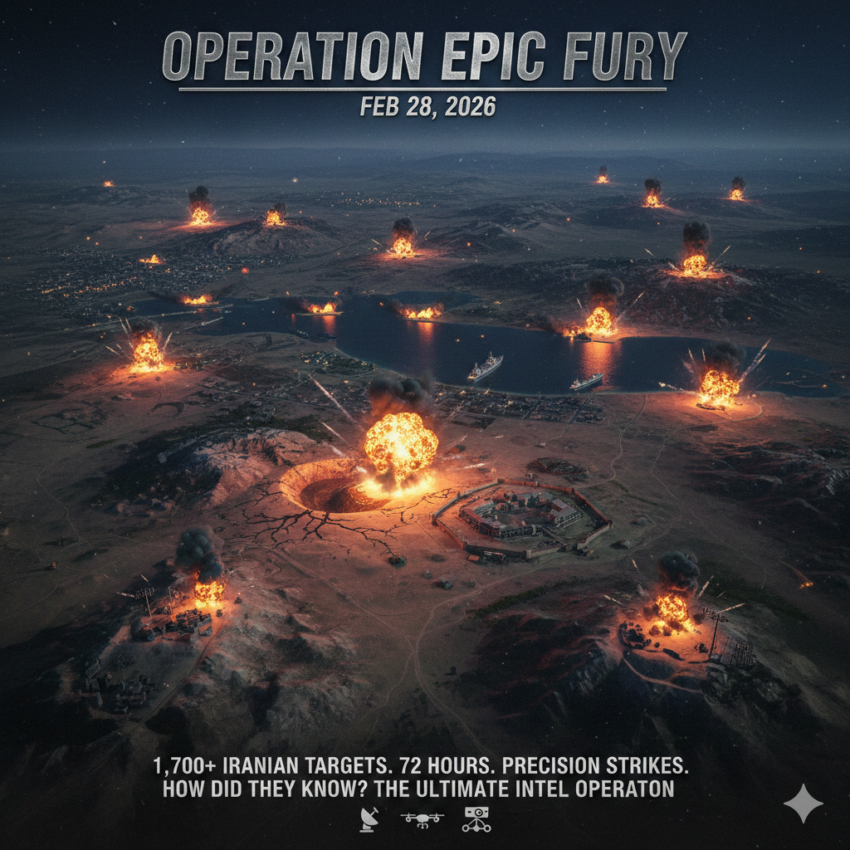
Operation Epic Fury, the joint U.S.-Israeli military campaign launched on February 28, 2026, struck over 1,700 Iranian targets within the first 72 hours, including deeply buried underground missile complexes, naval assets, command-and-control nodes, and even the compound of Supreme Leader Ali Khamenei himself. The sheer precision of the strikes — across hundreds of hardened, dispersed, and deliberately concealed Iranian military sites — raises a critical question that official briefings have barely scratched: How did the United States and Israel know exactly where to look?
The answer lies in one of the most sophisticated, multi-layered intelligence operations in modern history, assembled over years of preparation and drawing on every tool in the espionage arsenal.
Years in the Making
The intelligence picture that enabled Epic Fury was not assembled overnight. Defense analysts and former intelligence officers have noted that the U.S.-Israeli joint force entered this conflict with “a wealth of accurate targeting intelligence, based on espionage from overlapping sources” — a posture demonstrated as early as June 2025’s Operation Midnight Hammer. The targeting precision of that earlier operation, which struck Iranian nuclear sites, served as both a proof of concept and a rehearsal for the far broader campaign that followed nine months later.
Iran, for its part, provided inadvertent clues. In January 2026, the IRGC publicly unveiled an underground “missile city” at an undisclosed location, showcasing missiles including the KheibarShekan, Haj Qassem, and Sejjil ballistic missiles. Analysts note that such public displays — intended as deterrent theater — actually gave U.S. and Israeli intelligence a trove of observable data: equipment types, personnel, tunnel entrance configurations, and facility design signatures that could be cross-referenced against satellite imagery across Iran.
The HUMINT Breakthrough: Spies in a Denied Area
Human intelligence (HUMINT) inside Iran has historically been among the most difficult to collect. Iran has been what intelligence professionals call a “denied area” for the CIA since 1979, when the seizure of the U.S. Embassy in Tehran eliminated American diplomatic cover for clandestine operations. Without embassies or businesses to use as cover, running CIA case officers inside Iran carries existential risk — captured American spies face execution.
But the months leading up to Epic Fury saw an aggressive shift. As early as February 2026, the CIA was openly using social media platforms — including Tor-accessible channels — to recruit Iranian human sources, explicitly targeting individuals radicalized by Iran’s severe economic conditions and the wave of domestic protests that erupted in late 2025. This was not subtle tradecraft; it was deliberate, high-visibility outreach designed to cast a wide net among disgruntled military officers, scientists, and government workers who might provide “ground truth” that no satellite can deliver — the interior layout of hardened facilities, the schedules of senior officials, the morale of security forces.
The most dramatic HUMINT success was the killing of Ayatollah Ali Khamenei. According to reporting from RUSI, the CIA passed specific human intelligence to Israel regarding Khamenei’s precise location, intelligence so operationally valuable that the United States and Israel adjusted the timing of the entire operation to exploit the targeting window it opened. This single act of human intelligence — almost certainly sourced from a penetration agent within Khamenei’s protection detail or inner circle — illustrates how decisive a single well-placed spy can be.
Analysts also believe the CIA’s covert action program, reportedly arming anti-regime Kurdish fighters inside Iran, created an embedded network of personnel capable of conducting ground reconnaissance — almost certainly supported by Joint Special Operations Command (JSOC) deep reconnaissance troops operating in denied territory alongside CIA paramilitary officers.
SIGINT and Unit 8200: Listening to the Enemy Think
If HUMINT provided the human drama, signals intelligence (SIGINT) provided the operational backbone. The National Security Agency, the world’s most powerful SIGINT collector, played what one former NSA senior officer described as an “outsize role” in the Iran campaign. The NSA’s advantage is compounded exponentially by its partnership with Israel’s Unit 8200 — the Israeli military’s SIGINT directorate and its functional equivalent — which has spent decades cultivating deep access into Iranian military communications networks.
SIGINT serves two distinct functions in this conflict. Before strikes, it enables targeting by intercepting military communications that reveal where commanders are located, which facilities are operationally active, and what movements of personnel and equipment betray the positions of mobile assets. After strikes, it provides battle damage assessment (BDA) by eavesdropping on Iranian military and political communications as commanders scramble to report destruction to their superiors — telling the Americans precisely how much pain they have inflicted.
Critically, this created a painful dilemma for U.S. Cyber Command: every Iranian communications node destroyed removes a potential intelligence source. Pentagon Secretary Hegseth confirmed that U.S. Cyber Command served as “first-movers,” using “non-kinetic effects” to disable Iranian communications before the first bombs fell. But before that disruption, intelligence officers had to conduct classified “gain-loss” assessments to determine which communications nodes were worth more to destroy than to keep listening to.
GEOINT: Satellites, Underground, and the Muon Question
Geospatial intelligence (GEOINT) — the analysis of imagery from spy satellites — gave U.S. targeters a continuously updated visual map of Iran’s military infrastructure. Commercial satellite companies like Planet Labs and Maxar, whose imagery is freely shared with open-source analysts, have documented the physical signatures of Iranian military build-ups, tunnel construction, and equipment dispersal in publicly available form for years.
But Iran’s most critical military infrastructure — its ballistic missile complexes — was designed specifically to defeat overhead imagery. Carved into the granite of the Zagros Mountains, Iran’s underground launch bays and missile storage facilities lie beneath thousands of feet of rock. Traditional ground-penetrating radar reaches only 30–40 feet underground — a fraction of what is needed to map these facilities.
This is where speculation — grounded in documented U.S. defense research — becomes most intriguing. DARPA’s muon-based scanning program, known as MuS2 (Muons for Science and Security), uses cosmic ray muon particles that naturally penetrate kilometers of solid rock to essentially X-ray the interior of underground facilities. Analysis of the B-2 Spirit bomber strikes on “hardened ballistic missile facilities” — which required knowing the precise depth, orientation, and internal layout of these complexes for the GBU-57 Massive Ordnance Penetrator (MOP) to be accurately targeted — strongly suggests that some form of deep-penetration underground mapping was used. Whether the MuS2 program had been operationally deployed for this purpose remains classified, but former defense analysts have pointed to the operational indicators as circumstantial evidence of exactly such a capability being field-tested.
Cyber Espionage: Pre-Positioned for Years
Perhaps the most under-reported intelligence pillar is U.S. and Israeli cyber espionage — not the offensive disruption operations that made headlines, but the years of quiet network infiltration that preceded them.
RUSI researchers have noted that “cyber is almost certainly a critical capability in supporting reconnaissance and broader intelligence-gathering efforts in the months — and in this case, years — preceding an operation: mapping adversary networks; pre-positioning access within critical systems; and informing the planning of subsequent phases”. Israel’s pre-existing access to Iranian security camera networks and traffic camera infrastructure — demonstrated vividly in the operation to kill Khamenei, which involved hacking traffic cameras near his compound to track his movements — speaks to an intelligence architecture built over many years of patient, covert cyber access.
The disruption of mobile phone towers near Khamenei’s location — preventing his protection detail from receiving escape warnings — was not an improvised maneuver. It required pre-positioned access to Iranian telecommunications infrastructure, almost certainly established long before the operation began. This sequencing of HUMINT, SIGINT, and cyber espionage into a single, synchronized strike operation represented the most complex intelligence-to-kill-chain integration ever publicly documented.
The Israeli Contribution: Mossad’s Deep Penetration
No analysis of the targeting intelligence behind Epic Fury would be complete without emphasizing the Israeli contribution. Israeli intelligence — particularly Mossad’s human intelligence operations — has historically penetrated Iran far more deeply than the CIA has been able to. The 2018 Mossad theft of Iran’s nuclear archive from a warehouse in Tehran demonstrated an ability to run agents inside some of Iran’s most sensitive facilities. The same tradecraft was almost certainly at work in the months preceding Epic Fury.
Israeli military sources confirmed that intelligence units had “mapped the structure of the underground complex” at the nuclear facility struck in Tehran in early March, identifying personnel linked to its activities through a combination of high-resolution satellite imagery, signals intelligence, cyber surveillance, and human sources. The IDF has further confirmed that its intelligence apparatus monitored “construction projects, equipment transfers, and the movement of scientists linked to nuclear research” over an extended period to build the targeting picture.
The Unresolved Question
Despite the documented layers of HUMINT, SIGINT, GEOINT, cyber espionage, and allied intelligence sharing that collectively enabled Operation Epic Fury, significant questions remain unanswered. A Pentagon source reportedly told Congress in closed-door briefings that the official justification for initiating strikes — that Iran was planning a preemptive attack on U.S. forces — was not supported by available intelligence. This suggests the intelligence picture, however extraordinary in its technical depth, was also selectively interpreted to serve a predetermined political objective.
Former NSA officer John Schindler, writing in the Washington Examiner, offered a sobering reminder: the same intelligence community that enabled the precision targeting of Iran’s military also warned of the dangers of “unduly optimistic assessments” and the enemy’s vote in any conflict. Iran, he noted, had every incentive to employ denial and deception — hiding assets, feeding false signals, constructing decoys — just as Serbia did against NATO in 1999. How many of those 1,700 targets were hardened military assets, and how many were decoys or already-evacuated shells, remains a question that only post-conflict BDA will resolve.
What is beyond dispute is that the intelligence architecture behind Epic Fury represents the most sophisticated targeting enterprise in the history of warfare — a convergence of human spies, orbital sensors, quantum-era signal interception, cyber pre-positioning, and allied intelligence sharing that took not months but years to construct. The bombs, in a very real sense, were guided not just by GPS but by an intelligence machine that had been quietly mapping Iran’s military from the inside out, long before the first aircraft ever left the deck.